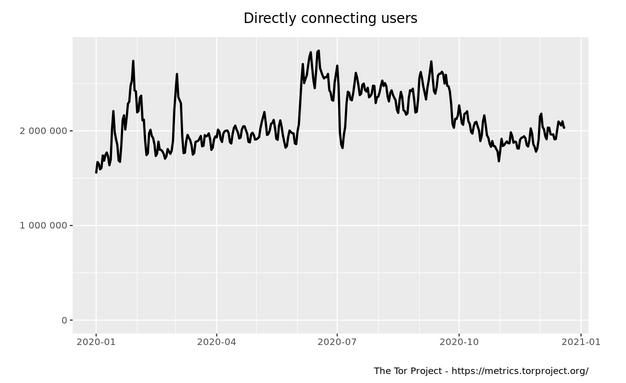
Anonymization technology is at the core of self-defense in the digital world. In this article, we take a look at the great anonymization project.
The underlying principle of Tor was developed in the mid-1990s by the United States to protect U.S. intelligence communications online.
25 years after its inception as a state-funded project, Tor is the most important adversary of state surveillance and the leader in distributed anonymization technologies.
It allows users to protect their privacy and circumvent censorship but also allows selling or buying illicit drugs. The Tor Project has been full of contradictions since the beginning.
Onion Routing
Tor aims to conceal its users’ identities and their online activity from surveillance and traffic analysis by separating identification and routing. It is an implementation of a technique called onion routing.
In an onion network, messages are encapsulated in layers of encryption, analogous to several peels of an onion. The encrypted data is transmitted through a randomly selected series of network nodes called onion routers, each of which “peels” away a single layer, uncovering the data’s next destination.
When the final layer is decrypted, the message arrives at its destination. The user remains anonymous to the service provider because each intermediary knows only the location of the immediately preceding and following nodes.
Deep and Dark Onion
The Tor software can be used in two ways: either as an anonymization service to accesses the regular internet or to access services in the virtual top-level domain “.onion”.
There are many misunderstandings and generalizations regarding the “.onion”. Let’s look at some subsets of the web and the naming first.
The SurfaceWeb is everything publicly available and accessible through search engines. This is where we find news sites, blogs like inversegravity, or shopping sites. The DeepWeb describes the parts of the internet that are hidden behind a login and therefore not publicly accessible. Examples are online banking sites or content behind a paywall.
The term DarkWeb describes services that require specific software to access them. Tor is such software and the TLD “.onion” is a major player in the so-called DarkWeb.
The hostnames under “.onion” are not actual DNS names, and the TLD is not registered in the root of the regular internet domain services. The purpose of the network is to hide both the identity of the service provider and the person accessing the service.
The mutual anonymity and the emergence of anonymous digital currencies created the possibility to buy and sell services and goods in complete anonymity.
Benefits worth the costs?
It is not without reason that stories about the Darkweb are popular in the media. There is everything that makes a good story, anonymous criminals engaging in illegal activities including sex and drugs.
Outrage from politicians and calls for regulation accompany many of these stories.
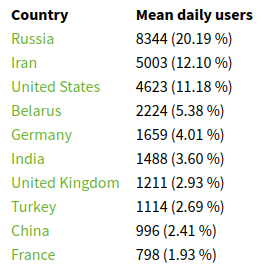
Though, a recent research article has shown that only ~6.7% of all Tor users are actually accessing Onion services for potentially illegal purposes.
The vast majority uses it as a privacy-enhancing tool to circumvent censorship or stay anonymous on the regular internet. Ultimately Tor is by its very nature dual-use and the question is if the benefits outweigh the costs.
On the 25th anniversary of Tor, there is no clear answer. The internet is a very young technology and we are grappling with the implications to personal freedom, censorship, human nature, social evil, and government policies.
Happy birthday Tor!